
AVC E-learning Center Activities: Academic Year 2017/2018
1 - Referendum
General Seminar was hold at AVC E-Learning Center on 19/9/2017 titled (Referendum) by the director of AVC E-Learning (Assist. Prof. Dr. Ismail Musa Murad), in this seminar he focused on the following items:
- Historical Notes
- Type of referendum in all Kurdish regions
- Kurdistani Sor (1922-1929)
- Arrat Mountain Republic (1922-1924)
- Iraq/Kurdistan Region (1970-1974)
- Kurdish Republic of Lagen 1992
- Rojava Region in Syria 2012

2 - Health & Safety
- On December 2017, employee Mrs. Dlxwaz Jabar participated in a workshop on Health and safety at SU and prepared a seminar on general health and safety
- The director of AVC center Dr. Ismail Musa prepared a seminar on general instruction and information on health and safety in general for our staff.
- On November 2017, Miss Suzan Aziz advanced researcher in our center worked on designing word cloud, to make some gallery on general referendum and general training course and expression on different items, which belongs to e-learning technology.

3- Prezi
- On December 2017, most of our technical staff participated in a seminar on Prezi software technology, which was hold by Mr. Soran Sabr Osman who holds MSC in oil and management.
4- Electronic Terrorism and Electronic Waste
- On May 2018, the director of AVC E-Learning Center Dr.Ismail Musa Murad introduced two seminar titled (Electronic Terrorism and Waste) for our staff. See attached file


AVC E-learning Center Activities: Academic Year 2018/2019
1- Training Course on Animation Technology
The 2nd Training Course titled Animation Technology in Education has been hold at our AVC E-learning Center for six SUE Colleges (College of Fine Art, Languages, Engineering, Law and Political Science, Islamic Science, Physical Education & Sport Science ) for the period of three days starting 23 – 25/10/2018.
The main purpose of the second training course on using animation technology in education and academics is to fulfill a cognitive function. Animations are intended to support students’ cognitive processes that ultimately result in them understanding the subject matter. Animation can be used to make very exciting and fun animations into which education and training can easily be incorporated. Instructors can also use animation to demonstrate things and concepts visually exactly how they want to since they have control of every aspect of the animation, so our AVC e-learning at SU intend to achieve for three days a general introduction on "Animation technology in Education" in cooperation with Institute of art in Erbil for the professors in our university due to that the animation can be an affective learning tool that attracts attention, engages the learner, and sustains motivation aspect. Such affective animation training is not focused on facilitating comprehension of any academic subject matter itself and often portrays activities that are interactive, creative, fun and motivational. Young students are fascinated by animation and animated stories and they enjoy the opportunity to create their own. The creative potential of animation is enormous, and integrating animation activities into the universities and school curriculum offers the possibility of tapping this potential to meet a range of educational objectives.
Benefits of animation as an effective learning tool
- Emphasizes development of students’ skills and understanding of creating and responding
- Enables students to apply Imagination & Rational Thinking
- Enables students to invent and explore multiple solutions to a problem
- Enables students to understand the value of reflection and critical judgment in creative work
- Fosters positive attitudes toward Art & Animation
- Introduces career possibilities

6- Seminar on E-waste was hold at Avicenna E-learning Center on 28/11/2018 by the Director of the AVC E-learning Center Dr. Ismail Musa Murad for the technical and educational staff
This seminar aims to review the issues relating to E-Waste. It identifies the sources of E-Waste as well as their components and the dangers in them. Alternative initiatives and means of managing E-Waste both nationally and internationally are discussed along with its effects on human health and environment. And also in this Seminar the Presenter focused on its necessary to establish a scientific team related to the subject in Kurdistan, in order to look after this Activity. Recommendations are made on appropriate treatment of E-Waste in order to make the environment safe for all.
1-Policy and Awareness: The state policy should be clearly documented and published. It is recommended to expedite the development of an e-waste set of guidelines and regulations.
2-Integrating with Solid Waste Management Strategy: e-waste management should be part of integrated waste management program of the country.
3-Data Base Management and Tracking: Further statistical analysis of data collected is recommended along with the use of earlier data.
4-e-waste specific Recycling Infrastructure: Development of recycling infrastructure is recommended for environmental improvement schemes.
5-Re-evaluate: Try finding one device with multiple functions.
6-Extend the life of your electronics. Buy a case, keep your device clean, and avoid overcharging the battery
7-Buy environmentally friendly electronics. Look for products labeled Energy Star or certified by the Electronic Product Environmental Assessment Tool (EPEAT).
7- Nanotechnology Workshop
The director of AVC E-learning Center at SUE (Assist. Prof, Dr. Ismail Musa Murad), participated in the second workshop on Nanotechnology at Ishik University –Erbil in December 23rd 2018
The following recommendations has been suggested as below:
1-Towards an international conference on aspects of nanotechnology activities in Kurdistan.
2-Focusing on the new researches on: Nanomaterials including Nanoparticles, Nanocrystals, Nano-porous materials, Nano tribology, Nanocomposites, Nano electronics, Nano-Magnetics, Nano biotechnology, Nanomedicine, Nanotubes/Nanowires/Quantum Dots, NEMs, MEMs, Nano-Fluidics, Nano-Sensors, Nano-robotics, Nano-Fabrication, Nano-Lithography, Nanotechnology for Energy, (Fuel cell, Solar cell, Hydrogen storage), Crystal Growth, Thin films, Ultrasonic, Solid State Ionics. And nnanotechnology: Risk Assessment and Management.
3- More training for development knowledge to provide workforce education and training in nanotechnology in order to develop advance basic to training programs taught by scientists and project/program for the undergraduate students.
4-In cooperation with IEEE nanotechnology council for arranging the largest conference and Exhibitions for the coming year here in Kurdistan.
5-More training for trainers (BSc. MSc and PhD) degrees should be hold in the near future on the fundamental of nanotechnology and its applications.
6-It is very necessary to establish a very new advanced modern lab with very well equipped with the modern demands related to research and training for the university.
The main recommendation as follow:
The main mission is to conduct high quality Nanotechnology field in Kurdistan, in order to achieve the following goals:
1-Towards an international conference on aspects of nanotechnology activities in Kurdistan.
2-Focusing on the new researches on: Nanomaterials including Nanoparticles, Nanocrystals, Nano-porous materials, Nano tribology, Nanocomposites, Nano electronics, Nano-Magnetics, Nano biotechnology, Nanomedicine, Nanotubes/Nanowires/Quantum Dots, NEMs, MEMs, Nano-Fluidics, Nano-Sensors, Nano-robotics, Nano-Fabrication, Nano-Lithography, Nanotechnology for Energy, (Fuel cell, Solar cell, Hydrogen storage), Crystal Growth, Thin films, Ultrasonic, Solid State Ionics. And nnanotechnology: Risk Assessment and Management.
3- More training for development knowledge to provide workforce education and training in nanotechnology in order to develop advance basic to training programs taught by scientists and project/program for the undergraduate students.
8- Seminar on Christams Comet: 46P Wirtanen
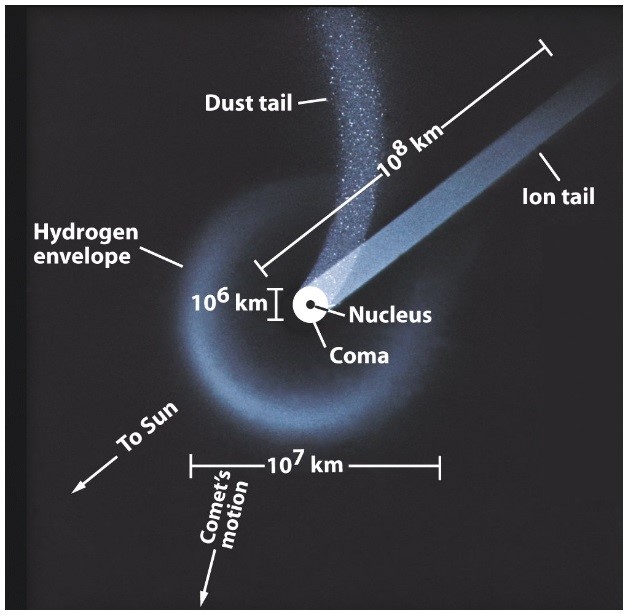
- Assist.Prof.Dr. Ismail Musa Murad the director of AVC e-learning center presented a seminar on the comet 46P/Wirtanen, which is the brightest comet of 2018 to pass the closest to Earth in December 2018. The presenter points that on December 16th Comet Wirtanen will be visible to the unaided eye. It makes the closet pass to us in over 400 years. The comet 46P/Wirtanen, which passes to Earth every 5.4 years, was one of three comets discovered by Carl Wirtanen in 1948 at the Lick Observatory in California. On January 15, 1948 Carl A. Wirtanen photographed a section of the sky at the Lick Observatory. Two days later, he realized that a comet was captured in the image. Comet 46P Wirtanen is a 1.2km diameter short period comet discovered photographically by Carl Wirtanen at Lick Observatory in 1948. Wirtanen is a Jupiter group comet that has a period of 5.43 years and aphelion of 5.1 AU. Perihelion is 1.05 AU and the orbit passes very close to the Earth’s orbit each perihelion. In the final months of 2018, Earth will experience what is probably the finest apparition of periodic comet (46P) Wirtanen of the 20th and 21st centuries. Comets are icy bodies in space that release gas or dust. They are often compared to dirty snowballs, though recent research has led some scientists to call them snowy dirtballs. Comets contain dust, ice, carbon dioxide, ammonia, methane and more. Astronomers think comets are leftovers from the material that initially formed the solar system about 4.6 billion years ago. Some researchers think comets might have originally brought some of the water and organic molecules to Earth that now make up life here. Comets orbit the sun, but most are believed to inhabit in an area known as the Oort Cloud, far beyond the orbit of Pluto. Occasionally a comet streaks through the inner solar system; some do so regularly, some only once every few centuries. He also explains the comet structure which contains of the following:
1. Nucleus: 10 km “Dirty Snowball” or "icy mudballs".
2. Coma: Cloud of evaporated ices and ions, may be 100,000 km in diameter
3. Tail: Always points away from Sun due to the solar wind and radiation pressure.
Astronomer Fred Whipple demonstrates the comet in general as “dirty snowball” model, while its chemical composition are a mixture of ices (both water and frozen gases) and dust . (relative to water) of carbon dioxide (CO2), carbon monoxide (CO), formaldehyde (H2CO), methanol (CH3OH), and methane (CH4).
Conclusion
The comets are the remainders of material formed in the coldest part of our solar system. Impacts from comets played a major role in the evolution of the Earth, primarily during its early history billions of years ago. Some believe that they brought water and a variety of organic molecules to Earth. Comets are important to scientists because they are primitive bodies left over from the formation of the solar system. They were among the first solid bodies to form in the solar nebula, the collapsing interstellar cloud of dust and gas out of which the Sun and planets formed, Over time a comet may become less active or even dormant. So in general the main importance of for studying the comet can be summarized as follow:
1. Comets usually travel through the universe for million to billions of years while being relatively unchanged. That allows it to gain some insights into the development of the universe.
2. Some people hope to find primitive life forms on those comets, e.g. bacteria.
3. Some comets are made of ice in which small particles (billions of years old) are included. That provides insight into the history of the universe.
9- One day workshop on the effect of mobile phones on kids
On 17th January 2019 one day workshop was presented at our AVC E-learning Center for the following Colleges of Salahaddin University:
Science, Education,Basic Education, Agriculture and ....
In a three hour period Workshop more than 72 Professors attended.
The presenter (Dr. Ismail Musa Murad the director of the Center) of this workshop points that today's children and teenagers are growing up immersed in digital media. They are exposed to media in all forms, including TV, computers, smartphones, and other screens. Because media can influence how children and teens feel, learn, think, and behave. The effect of mobile phone radiation on human health is a subject of interest and study worldwide, as a result of the enormous increase in mobile phone usage throughout the world. Other digital wireless systems, such as data communication networks, produce similar radiation as well.
He added that the mobile today is something very important in our daily lives, and given services provided by the individual behind many of the impact of mobile phone on children's behavior? Questions came as follows:
1-What are the habits of the use of child mobile phone?
2-What are the reasons and motives that led these children to the use of modern technology?
3-What are the different aspects of mobile phone use for children?
This workshop aims to identify the effects left by mobile phone on children, we have adopted the descriptive survey method, which is the most suitable and appropriate for such studies, and we have adopted in the collection of information on the two tools questionnaire and interview tool inside the schools in order to look for output data. Mobile phones emit radiofrequency energy, a form of non-ionizing electromagnetic radiation, which can be absorbed by tissues close to the phone. The amount of radiofrequency energy a mobile phone user is exposed depend on many factors as the technology of the phone, the distance between the phone and the.
The side effects of using mobile phones cause dozens of tweets that can lead to eyestrain, blurred vision, dizziness, and dry eyes. And blurred vision plus sore neck muscles can also cause headaches. Cell phones radiation are harmful and may be dangerous, the science is still out on whether the long-term use of cell phones-which emit electromagnetic radiation when they send and receive signals from towers or Wi-Fi devices can affect human health. Many studies have shown that the effects of cell phone radiation and over-exposure to the human body can adversely affect cell health. The electromagnetic radiation (EMR) emitted by cellphones can cause our cells to heat up and become damaged over time.
Children can be seen handling mobile phones and smartphones all around the world. Older children can be seen talking to their friends for long hours, while others might spend their time playing countless games on the phone. The utility of the device cannot be debated. However, continued use and exposure to the phone can have harmful effects on the child. With children, we have reason to be especially careful, because there is not enough research on children's mobile phone use. Unfortunately, it will not be easy to obtain this information in the future, either, because of ethical considerations, the use of children as research subjects must always be heavily justified"

The presenter also recommended to limit media use due to that overuse of digital media and screens may place your child or teens at risk of sleep problems. Kids and teenagers who spend more time with social media or who sleep with mobile devices in their rooms are at greater risk for sleep problems.
Children who overuse online media can be at risk for problematic Internet use besides the negative effect on school performance, and also risky behaviors.
Since tomorrow’s problem are developing today, so a vision for the future our decision today will have a significant effect tomorrow.
Distance Is Your Friend
2. Avoid Using Your Cell Phone When The Signal Is Weak
3. Avoid Carrying Your Cell Phone on Your Body at All Times
4. Children Should Only Use Cell Phones For Emergencies
5. Do Not Sleep With Your Cell Phone Powered On
In Kurdistan: A new national law should ban WI-FI in schools
We hope that in 2019, Kurdistan should passed a landmark law that calls for precaution with wireless devices for kids, children in the kindergarten and schools, and the general public
1. Wi-Fi should be banned in schools
2. Wi-Fi routers should be turned off in school when not in use
3. Most citizens will have access to environmental cell tower radiation measurements near homes
4. There will be continued research conducted into health effects of wireless communications
5- The Kurdistan parliament should take some steps and should recommended an education program to alert pupils to the potential dangers of mobile phone use
6- We strongly advise limited use of cell phones, and other similar devices, by young Kids, children and teenagers
7- Scientists view about the dangers of mobile phones
8- Dangers of Wi-Fi and other wireless technology in general
9- Follow the opinion of physician and parents to limit the overuse of mobile phone, due to that the decisions we make to day may have far reaching consequences in the future for our kids
To Reduce Cell Phone Radiations
Research on the influence of mobile phone on our school today has not been given much attention. There is the conflicting priority of young people, parents, teachers, and professors in relation to the mobile phone device such as discipline in the classroom and parents worried about means of contacting their children at every point in time.
The Kurdish people have also joined the rest of the world on Facebook, Twitter, Yahoo, Gmail, and Google besides with quite a huge number of them visiting the sites daily. Kurdish nation are so active in these sites that some of them are considering their sites for Kurds all which would not have been possible without affordable internet services offered by mobile Phones operators. A large number of Kurdish make honest living on the internet as web publishers, bloggers, apps developers, internet security consultants, social media consultants, and online marketing consultants.
The benefits of mobile phones integration into student learning on campus are useful with the mobile phone capabilities that are easily supporting learning. Which are: SMSs (text messaging): Short Message Services allow users to send/receive messages of up to 160 characters between mobile phones.
MMSs: Multimedia Messaging Service serves the same purpose as SMSs, but it allows the inclusion of graphics.
Kurdistan Ministry of Education should issue new guidelines regarding to limit Wi-Fi use in schools. The guidelines will:
Recommendations for schools
The following recommendation can summarized as follow:
1-Stop the installation of wireless networks in classrooms and in kindergarten
2-Limit Wi-Fi use, especially in younger grades. Cell phones stay off and in the backpacks during class and on the campus during school hours
3- To lead to less EMF emissions and safer wireless devices, there should be support efforts by authorities and governments to provide independent standardized transparent research to define safe limits in all the different wireless frequencies used commercially
4- Desktop computers and power supplies be kept at a distance at least 20 cm from students
Finally, this workshop found the following results: a mobile phone that has a double-edged positive and usurped weapon effects through its impact on children's behavior.
10 - One Day Workshop on Cyber Extortion ( Electronic Extortion )
On 17/2/2019 the director of AVC E-learning Center (Dr. Ismail Musa Murad) arranged a one day workshop and presented under the titled: “Cyber Extortion” at AVC E-learning center at SUE for six colleges (Education, Basic Education, Agriculture, Art and Language). The number of participants 80 College Lecturers.
Upon completion of this seminar, you should be able to:
1-Understand the need for information security
2-Understanding types of extortion and cyber or internet extortion
3- Attention to strangers offering help
4- To clarify roles and responsibilities and to divide authority between the government and private sector in case of a cyber-security emergency
5- Can disrupt our freedoms and economy
Cyber extortion is a growing and rapidly evolving risk. The Cybersecurity enhancement act of calls for an extensive public and private collaboration on preparedness and restoration, the promotion of cyber-security public awareness, education and precaution for the public especially (Kids ,teens).
The purpose is to clarify roles and responsibilities and to divide authority between the government and private sector in case of a cyber-security emergency.
As cyber blackmail, internet extortion, computer extortion or electronic extortion, such as personal photos or videos, demanding payment to stop them from. These webcam videos are recorded by the criminals who then threaten to share the images with the victims' friends and family. Increasingly sophisticated and well-organized cyber-criminals are attempting to steal our identities, money, business innovations and even our national security secrets. Make no mistake about it: We are under attack—you, me.
What can be done right now to help prevent this new form of cyber extortion
- Use software to monitor teenager’s social media and email accounts
- Informing teenagers about cyber extortion and that they may encounter it
The most common form of cyber extortion is ransom malware, or ransomware, which prevents users from accessing information, and demands payment to gain access to it. This seminar then goes on to give instructions on how to act if you are a victim of cyber extortion and security recommendations to prevent cyber-attacks.
In case of receiving a threatening email risk Management Solutions can be useful as follow:
1-Immediately report it to your firm's IT department and the extortion attempt reported to the FBI cyber-crimes unit
2-Never open attachments that claim to show your confidential information, do not reply, and never send money - in any form
3- It is important to stop and think before responding to requests for, or posting, personal information
4- Never use the name of a family member (or a pet for that matter) in any password
5-Never use the same password for access to more than one account
6-Do not communicate with cyber criminals
11- One day Seminar on Cyber Terrorism
Cyber Terrorist
This seminar about Cyber Terrorism was hold by the director of AVC E-learning Center Dr. Ismail Musa Murad on 2/4/2019 at the College of Education Physics Department for the Lecturers of Physic Department.
- Address the phenomenon of cyber terrorism and to minimize its risks and its consequences in general request.
- Address early history of terrorism.
- What the internet offers to terrorists in this era.
- Advertise part of the cyber terrorist organizations all over the world
What is meant by “Computer Security”?
- Computer based
- Poor passwords
- Lack of appropriate protection
- Network based
- Unprotected or unnecessary open entry points
- Information Technology as a Weapons or Target

1-Terrorist groups have used computer technology to threaten or attack national security infrastructures, and commercial firms.
2- These attacks have reportedly generated actual damage only in form of disruption of services, public inconveniences, or financial loss.
3-The technology also creates 3-D images of contents to allow screeners to get a full and rotatable view of objects.
How to protect yourself against cyber crime
Anyone using the internet should exercise some basic precautions. Here are some tips you can use to help protect yourself against the range of cyber crimes out there.
1. Use a full-service internet security suite
2. Use strong passwords
3-Don’t repeat your passwords on different sites, and change your passwords regularly. Make them complex. That means using a combination of at least 10 letters, numbers, and symbols. A password management application can help you to keep your passwords locked down.
The Physics of Lightning
On 18th April 2019 a Seminar about the physics of lightning was hold by the director of AVC E-learning Center Dr. Ismail Musa Murad at the AVC E-learning Center for the staff of AVC Center. In this Seminar different topics about lighting was discussed. How to behave in case of a strong lightning, the different types, and also how it is created. Along with videos for how to avoid the effect of lightning and thunder was shown.
Lightning is a sudden electrostatic discharge during an electrical storm. This discharge allows charged regions in the atmosphere to temporarily equalize themselves, when they strike an object on the ground. Although lightning is always accompanied by the sound of thunder, distant lightning may be seen but be too far away for the thunder to be heard.
There are three types: Lightning can take one of three forms).
1-There is intra-cloud lighting (IC), which takes place between electrically charged regions of a cloud;
2-Cloud-to-cloud (CC) lighting, where it occurs between one functional thundercloud and another;
3-Cloud-to-ground (CG) lightning, which primarily originates in the thundercloud and terminates on an Earth surface

How to avoid Lightning
Take extra precaution during thunderstorms to avoid getting struck and try to follow the following steps:
- Avoid swimming or watersports on rainy days.
- Run to your vehicle for safety.
- Staying safe Indoors
- Avoid bathing, showering, or using the sink as much as possible.
- Pull to the side of the road in heavy storms.
- To avoid using any plugged-in electronics.
- Don't handle the radio or your GPS system.
- Keep your windows closed.
- Staying Safe in a car and run to your vehicle for safety.
- Avoid metal objects, like fences or exposed pipes
- Add a lightning rod to your roof.
- Do not use the elevator.
- Use stairs if they do not have a metallic handrail.








